- Joined
- Nov 6, 2003
- Messages
- 44,860
- Reaction score
- 30,569
Update December 2018: The two free products in this thread are discontinued or End-of-Life, making this thread mostly obsolete.
1. Malwarebytes Anti-Exploit has been discontinued and is only available as part of the paid Malwarebytes Anti-Malware Premium (for home use) and Malwarebytes Endpoint Protection (for business). I have zero affiliation with Malwarebytes and will not use SDN as a platform to push their paid products.
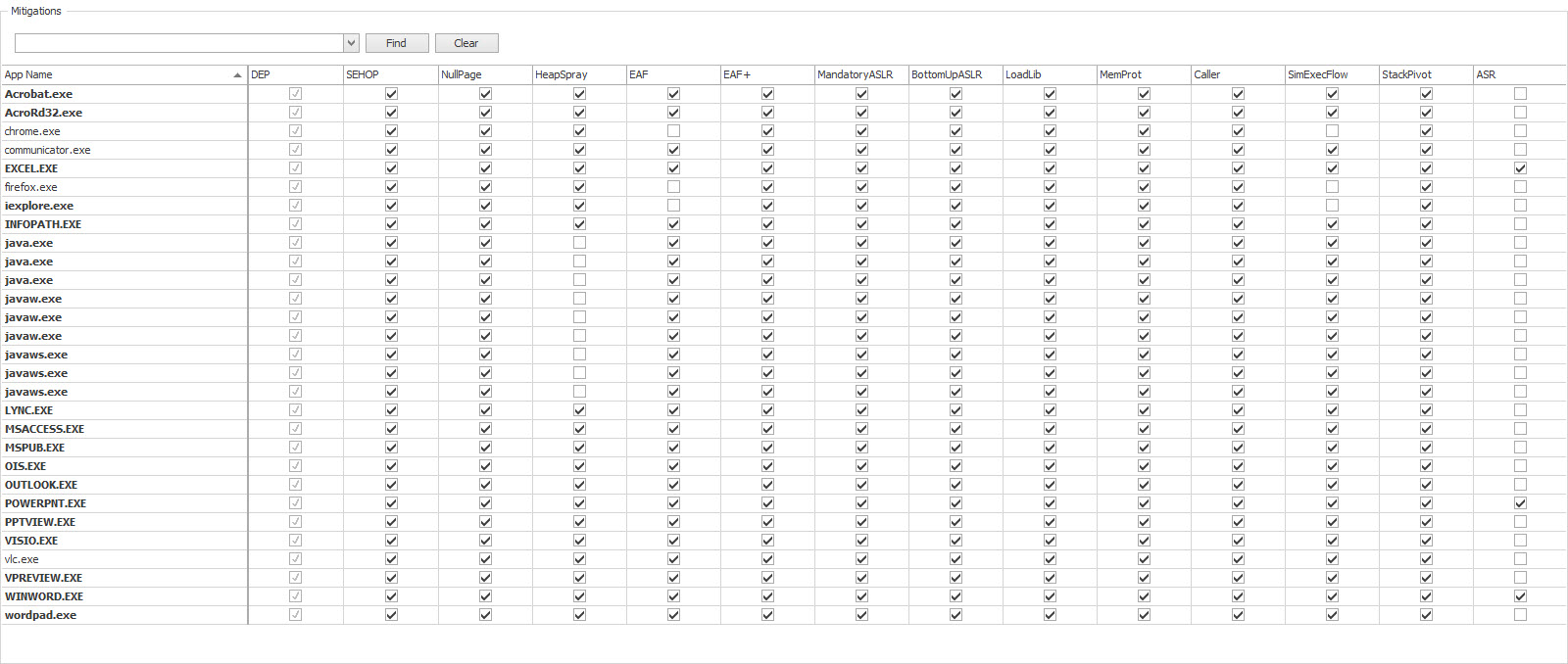
2. Microsoft Enhanced Mitigation Experience Toolkit (EMET) 5.52 is now End-of-Life, and Microsoft has discontinued support for it. It is still free and valid for Windows 7 and Windows 8.x, but it no longer works in Windows 10. Instead, Windows 10 has incorporated some/most of EMET's functionality into Windows Defender Security Center --> App & browser control --> Exploit protection --> Exploit protection settings. Modifying these settings is for advanced users only.
Source: https://support.microsoft.com/en-us/help/2458544/the-enhanced-mitigation-experience-toolkit
----------------------- Original Thread from 2015 ----------------------------
tl;dr: This thread is not about anti-virus or anti-malware but about hacking prevention tools that work side-by-side your antivirus/anti-malware tools.
Note: Only do this on your personally-owned computers or systems with which you are authorized.
Sup? I haven't geeked out in this forum in a bit, but I finally learned some things I'd been meaning to learn about for a long time and wanted to share with you just how stupid easy it is to add some layers of protection to common Internet-facing applications we all run on our machines, namely web browsers.
Nowadays, many hacking attempts, attacks, and exploits occur against weaknesses (think of them as aneurysms in your applications) in web browsers and other Internet-facing applications. If a website -- even a legitimate one -- is compromised, it can be used as a vector to deliver malware into your computer or a direct injection of an undocumented method to break into your machine and take control of it.
<Large part of original post redacted due to outdated information>
1. Malwarebytes Anti-Exploit has been discontinued and is only available as part of the paid Malwarebytes Anti-Malware Premium (for home use) and Malwarebytes Endpoint Protection (for business). I have zero affiliation with Malwarebytes and will not use SDN as a platform to push their paid products.
2. Microsoft Enhanced Mitigation Experience Toolkit (EMET) 5.52 is now End-of-Life, and Microsoft has discontinued support for it. It is still free and valid for Windows 7 and Windows 8.x, but it no longer works in Windows 10. Instead, Windows 10 has incorporated some/most of EMET's functionality into Windows Defender Security Center --> App & browser control --> Exploit protection --> Exploit protection settings. Modifying these settings is for advanced users only.
Source: https://support.microsoft.com/en-us/help/2458544/the-enhanced-mitigation-experience-toolkit
Microsoft said:End of Life Statement
We have listened to customers' feedback regarding the January 27, 2017 end of life date for EMET and we are pleased to announce that the end of life date is being extended 18 months. The new end of life date is July 31, 2018. There are no plans to offer support or security patching for EMET after July 31, 2018. For improved security, we recommend that customers migrate to the latest version of Windows 10.
----------------------- Original Thread from 2015 ----------------------------
tl;dr: This thread is not about anti-virus or anti-malware but about hacking prevention tools that work side-by-side your antivirus/anti-malware tools.
Note: Only do this on your personally-owned computers or systems with which you are authorized.
Sup? I haven't geeked out in this forum in a bit, but I finally learned some things I'd been meaning to learn about for a long time and wanted to share with you just how stupid easy it is to add some layers of protection to common Internet-facing applications we all run on our machines, namely web browsers.
Nowadays, many hacking attempts, attacks, and exploits occur against weaknesses (think of them as aneurysms in your applications) in web browsers and other Internet-facing applications. If a website -- even a legitimate one -- is compromised, it can be used as a vector to deliver malware into your computer or a direct injection of an undocumented method to break into your machine and take control of it.
<Large part of original post redacted due to outdated information>
Last edited: